The next time you’re on a bus or at an airport, it’s a good idea to think twice before using or borrowing someone else’s USB cable.
But WHY?
Because that simple-looking USB cable could be a secret hacker tool called O.MG Cable!
In this article, “How to Identify a Hacked O.MG Cable”, I’ll tell you all about this cable that looks normal but can be used by hackers to steal your information or mess with your device.
I’ll also share some tips on spotting these cables and best security practices for keeping your device safe. So, let’s get started –
TL;DR
2). The features of O.MG Cables, such as creating a Wi-Fi hotspot and executing scripts remotely, are explained.
3). The difficulty in spotting these cables due to their close resemblance to standard USB cables is discussed, highlighting that careful observation can still identify them.
4). The use and benefits of an OMG cable detector for identifying these cables are presented.
5). The overall theme emphasizes the importance of vigilance and informed awareness to protect oneself from such hidden threats.
What is an O.MG Cable?
The O.MG Cable is a handcrafted USB cable that contains a sophisticated implant, enabling it to serve as a covert data collection and exfiltration device. It is primarily used by Red Teams (simulation attackers in cybersecurity) to emulate potential hacking scenarios.
The cable can function as a keylogger, record keystrokes, perform injection attacks via DuckyScript, and facilitate data exfiltration to a remote server. Notably, the O.MG Cable is designed to appear like a standard USB cable, making it practically unnoticeable.
The product has various options, with different tiers: Basic, Plus, and Elite/Early Access. The cable types available are USB-A, USB-C, and Directional C to C. It also offers passthrough ends in Black or White for Lightning, USB-C, and MicroUSB.
Please note that the covert nature of the device may provide opportunities for misuse by bad actors.
Features of OMG Cable
Below are ten unique features of the Hak5 O.MG Cable:
- Indistinguishable Appearance: The O.MG cable is essentially a USB cable with a hidden implant, making it look like a normal cable.
- Creates a Wi-Fi Hotspot: The O.MG Cable can create a Wi-Fi hotspot to connect with a hacker’s device.
- Scripting Support: This cable allows users to generate payloads (scripts) for various tasks and execute them automatically.
- Remote Payload Control: You can remotely change the payloads on the fly.
- Enhances Remote Execution: It is built for enhancing remote execution with stealth and forensics evasion.
- LED Status Indicator: It comes with an LED that is helpful for quick visual feedback while testing and deploying.
- Data Exfiltration Capable: It can store scripts in onboard memory and retrieve the results later.
- Can be Programmed to Self-Destruct: To avoid detection, it can be programmed to self-destruct, wiping its memory.
- Detach Mode: In this mode, the cable works like a normal USB data/power cable and disconnects from the Wi-Fi.
- Microcontroller-Based: The O.MG Cable uses a microcontroller, making it flexible and customizable for various purposes.
It’s important to note that while these features make the O.MG Cable powerful, they should be used responsibly and ethically.
Is It Impossible to Spot O.MG Cable?
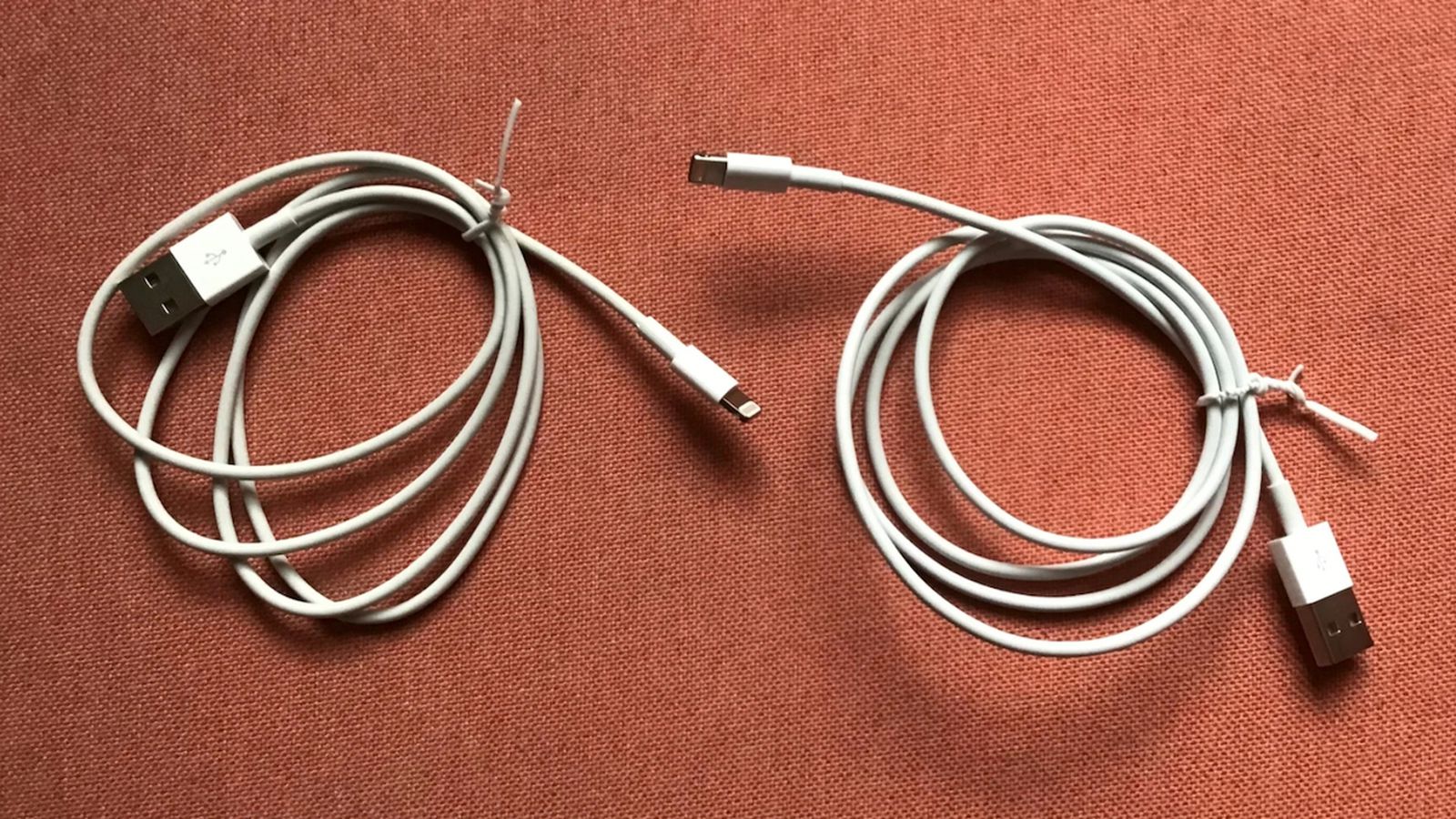
It is not impossible to spot an O.MG Cable, but it can be difficult due to its design closely resembling standard USB cables.
However, with closer inspection, you might notice certain differences between an O.MG Cable and a standard USB cable.
For example, one side view comparison shows that the O.MG Cable has a seam on its side, which may be due to the assembly process being different from that of a standard USB cable.
Another guide notes that Apple cables typically have a matte finish on the USB connector, whereas the O.MG Cable has a glossier finish. Also, the connector pins on the Apple cable appear to be thinner.
Although it might not be evident at first glance, with a keen eye and knowledge of these distinguishing features, it is possible to identify an O.MG Cable.
How to use an OMG cable detector?

You can use the Hak5 O.MG Cable Detector in the following manner:
- Plug the USB Cable: You start by inserting the USB cable you want to inspect into the detector.
- Connect to the Computer: Connect the O.MG Cable Detector to your computer’s USB port.
- Indicator Lights: Look out for the indicator lights. The LED activity on the O.MG Cable Detector indicates signs of life.
- Analyze the Result: If the indicator light shows any activity, there is some power or data traffic through the cable. This is unusual for a standard USB cable just used for charging and can indicate that the USB cable is malicious.
Do note that the Detector analyzes the cable behavior 200,000 times per second through side-channel power analysis.
Does Hak5 O.MG Cable Really Work?
Yes, the Hak5 O.MG Cable does work as advertised, according to the information publicly available online.
Hak5 describes the O.MG Cable as a “handmade USB cable with an advanced implant hidden inside”. It’s designed to help Red Teams emulate sophisticated attack scenarios. At first glance, it looks like any other USB cable, making it an effective tool for penetration testing.
However, upon closer inspection, one would discover it’s a clever hacking device. It can create its own Wi-Fi hotspot, which hackers can connect to from their computer. Once connected, the hacker can start recording keystrokes.
The Hak5 forum provides additional support and details on troubleshooting the O.MG Cable.
In short, the Hak5 O.MG Cable works and is an effective tool for penetration testers and cybersecurity professionals. However, you should use it by ethical principles and compliance with legal regulations.
Where to Buy Hak5 O.MG Cable Detector?
You can purchase the Hak5 O.MG Cable Detector directly from the Hak5 online store. The product is called “Malicious Cable Detector by O.MG” and is available at this link.
Tips to Prevent Hacking From an O.MG Cable

To prevent hacking from an O.MG Cable, follow these tips to ensure safety and protect your devices:
- Inspect physical cables: Examine USB cables for any discrepancies or signs of tampering, paying attention to any unusual seams, shiny USB connectors, or differences in the thickness of the connector pins.
- Use your own cables: Bring your own USB cables when charging at airports, cafes, or other public locations to reduce the risk of using compromised cables.
- Avoid using unknown or borrowed cables: Be cautious when borrowing cables from friends or acquaintances. Instead, carry your own cable or purchase a new one from a reliable source.
- Educate yourself and others: Increase awareness amongst your peers and colleagues about the risks and potential threats of using compromised USB cables.
- Establish strong security protocols: Implement secure device management policies in corporate settings to prevent unauthorized devices from connecting to your network.
- Invest in protective tools: Consider using a USB data blocker or Hak5 O.MG Cable Detector that physically blocks data transfer while allowing charging, preventing any potential hacks using an unknown cable.
- Keep devices updated: Regularly update the firmware and software on your devices to minimize vulnerabilities that hackers could exploit.
- Follow best security practices: Use strong passwords, activate two-factor authentication, and secure your wireless networks to protect the overall security of your devices.
- Monitor devices for suspicious activity: Regularly check your devices for any unusual activity, such as unauthorized connections or sudden changes in settings. Consult an IT professional if you suspect that your device has been compromised.
- Create a trusted device policy: Maintaining an inventory of approved USB cables and devices in corporate environments. Educate employees on the risks of using unauthorized cables and encourage them to report any suspicious equipment immediately.
Following these tips can reduce the risk of hacks from malicious USB cables like the O.MG cable.
Conclusion
Understanding the risks posed by hacked USB cables like the O.MG Cable is essential for keeping our devices and personal information safe.
I’ve explored how such cables can compromise the security of our devices and what you can do to spot them and protect yourselves.
Remember to stay on your toes when using or borrowing USB cables, and follow the tips and recommendations in this article.
By doing so, you’ll save your device from getting compromised.